 Last week a massive ransomware outbreak impact millions of computers and exposed weaknesses in Microsoft's Windows operating system. The latest attacks are known as "WanaCryptor", "WeCry", or "WeCryptor." Major corporations found weaknesses within their systems, which poses a threat to several industries including healthcare.
Last week a massive ransomware outbreak impact millions of computers and exposed weaknesses in Microsoft's Windows operating system. The latest attacks are known as "WanaCryptor", "WeCry", or "WeCryptor." Major corporations found weaknesses within their systems, which poses a threat to several industries including healthcare.
If you are the victim of a Ransomware attack you probably have three ways to react.
- Enter safe mode. Disconnect your PC from the Internet and begin the cleaning process before you connect to the Internet again. Disconnecting will aid in reducing the risk of having the malware spread. Shut down and re-boot your PC in safe mode. If malware is on your system, safe mode will prevent it from running. Once you are in safe mode start the cleaning process by deleting the temporary files and then run a disk cleanup.
- Restore your system to original settings. Restoring your system will delete all the data and makes the computer seem brand new once again. Install a malware detection program along with anti-virus to regularly scan and protect your computer.
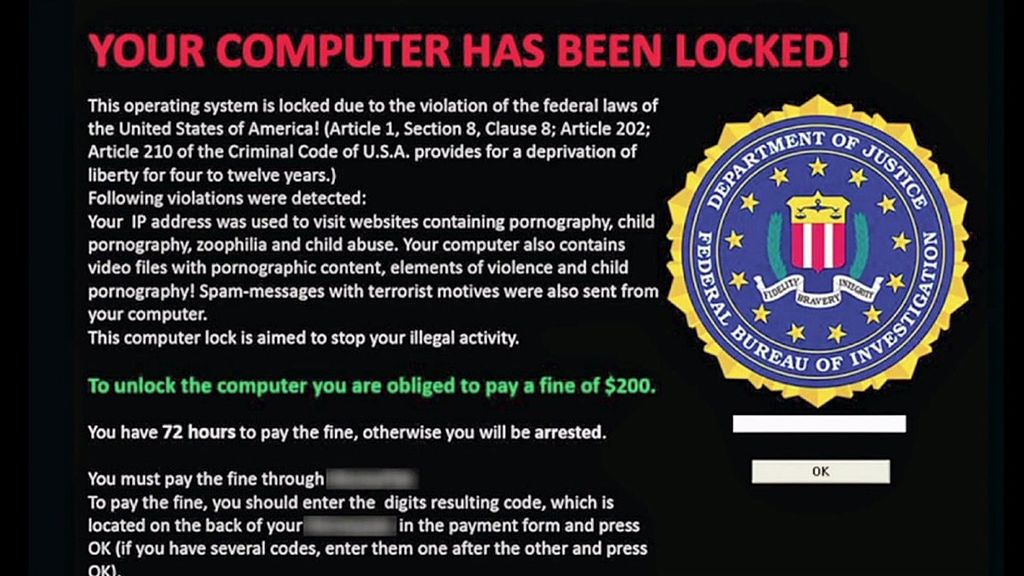
- Pay per the illicit demand. Never do this. (Some take the position that as a last resort before compromising patient care payment must be made. If faced with this dilemma, consider the possible downside outcomes; the extortionist may not unlock anyway and your practice leaves itself open to further illicit demands in the future).
So, if after the fact these three choices seem not good, bad, and terrible, what should you be doing to avoid having to make them?
Obviously, backing up your system (test to be sure the backup is working) regularly is a critical procedure that should be set to occur automatically (even if you are using secured cloud services, you still have liability for a ransomware attack). Therefore, do this simple thing; back your system up and secure the backup media whatever it might be.
Here are some other ideas that help avoid the attack in the first place:
- Conduct a Security Risk Analysis (SRA).
- Install trusted anti-virus, anti-malware software. Set the software to run regular system scans. Without scanning, the programs are not going to be as effective in detecting malware.
- Most attacks are made possible by employee error. Your staff must use their computer access only for practice sanctioned activities. Employees need regular training reguarding attachments and downloading from the Internet. It is import to communicate the danger of unverified links, and never allow staff to use a USB device that is not trustworthy.
- Consider using whitelisting software to restrict systems from running software or accessing certain websites unless they have been approved by management.
- Maintain a current operating system. Following the recent attack Microsoft began offering free upgrades to Windows 10. The latest system upgrades are programmed with tools needed to protect your system against malware.
- Do not rely solely on encryption. If a hacker has a valid login, encryption is useless.
- Training has to stress that personal information as well as Protected Health Information (PHI) can be put at risk exposing the practice to possible claims for damages due to identify theft in addition to HIPAA penalties.
So how freaked out should you be about ransomware? Enough to take preventative steps. Is an attack by a hacker completely avoidable? Probably not, but you can take steps to protect your system and potentially save your company hundreds of thousands or millions of dollars in fines by protecting healthcare records with proper security measures. For additional information about ransonware in the healthcare industry, subscribe to our weekly newsletter. Healthcare Compliance Pros specializes in providing year-round expert support for HIPAA, OSHA, HR, and Corporate Compliance programs.

